Unknown Facts About Safeguarding Data Privacy And Security
Table of ContentsUnknown Facts About Safeguarding Data Privacy And SecurityHow Safeguarding Data Privacy And Security can Save You Time, Stress, and Money.Fascination About Safeguarding Data Privacy And SecuritySafeguarding Data Privacy And Security Things To Know Before You BuyThe Only Guide to Safeguarding Data Privacy And Security
It offers the safety of cryptographic secrets by handling the generation, exchange, storage space, deletion as well as updating of those keys. This is done in order to keep delicate information safe and secure and also stop unauthorized gain access to. Key management is also made use of to make certain that all customers have accessibility to the best keys at the right time.With key monitoring, firms can likewise track who has actually accessed which tricks as well as when they were used. GRC is a set of plans as well as processes that a firm utilizes to achieve its business objectives while handling risks and also conference relevant governing needs. GRC assists a company's IT group to align with the business purposes as well as guarantees that all stakeholders know their obligations.
By utilizing verification as well as authorization devices, organizations can make certain that only accredited individuals have access to the sources they require while still protecting the data from being misused or swiped. It likewise aids in checking user task and making certain compliance with business policies as well as procedures. No Trust fund is a security structure requiring all individuals, whether in or outside the company's network, to be verified, accredited and constantly confirmed for safety and security arrangement and pose prior to being granted or keeping accessibility to applications and data.
The Best Guide To Safeguarding Data Privacy And Security
By overwriting the information on the storage space gadget, the information is made irrecoverable and achieves information sanitization. Data resiliency is the procedure of producing backup copies of electronic data and also various other company details to ensure that organizations can recoup the data in instance it's harmed, deleted or swiped during an information breach.
The The Golden State Consumer Personal Privacy Act (CCPA) was introduced in 2018 to permit any type of California customer to require to see all the info a company has actually saved on them, in addition to a full listing of all the third celebrations with whom that data is shared. Any type of firm with at least $25 million in revenue that serves The golden state locals have to adhere to CCPA.
The 8-Minute Rule for Safeguarding Data Privacy And Security
The Health And Wellness Insurance Portability as well as Liability Act (HIPAA) is a united state policy enacted in 1996 that set national requirements to secure delicate person health information from being disclosed without the client's approval or expertise. HIPAA covers the defense of independently recognizable wellness details covered by 3 sorts of entities: health insurance plan, wellness treatment clearinghouses, and also healthcare service providers who conduct the basic healthcare transactions electronically.
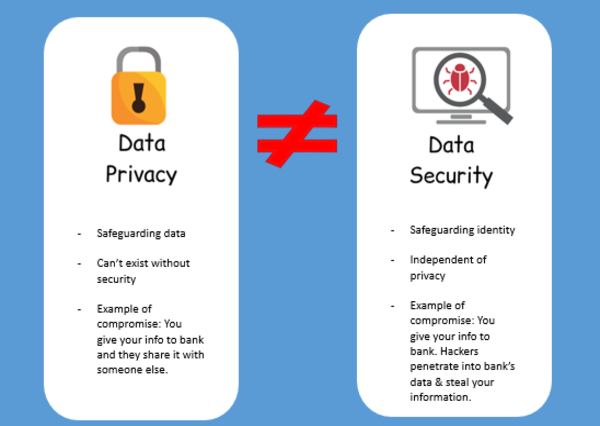
In today's increasingly linked globe, where modern technology has actually ended up being an essential part of our lives, the importance of data personal privacy and also data protection can not be overstated. As people, companies, as well as governments generate and also take care of huge amounts of data, it is crucial to recognize the requirement to safeguard this information and also protect the privacy of those it worries.

See This Report about Safeguarding Data Privacy And Security
The data collected is different for different businesses. Companies require to refine this high-volume details to resolve their service challenges.: It is the rate at which data is produced and collected.
Predictive evaluation permits services to check as well as evaluate social networks feeds to comprehend the sentiment among consumers. Firms that collect a huge amount of data have a much better chance to check out the untapped area together with carrying out a more profound and also richer evaluation to profit all stakeholders. The try this out faster and better a business recognizes its client, the greater advantages it enjoys.
The Hevo platform can be established in simply a few mins as well as requires marginal maintenance.: Hevo supplies preload changes via look at these guys Python code. It likewise allows you to run makeover code for every event in the pipes you established. You require to edit the residential properties of the event things gotten in the transform technique as a parameter to perform the change.
Safeguarding Data Privacy And Security Fundamentals Explained

However, the dangers involved are rapid with safety and security concerns. Also the tiniest error in regulating the accessibility of data can enable any person to get a host of delicate information. Consequently, big tech companies welcome both on-premise and Cloud Data Storage space to get safety in addition to versatility. While mission-critical info can be stored in on-premise databases, much less sensitive information is kept in the cloud for simplicity of use.
It increases the expense of taking care of data in on-premise data sources, business must not take protection threats for approved by saving every information in the cloud. Fake Data generation postures a serious threat to businesses as it eats time that otherwise might be invested to determine or fix other pressing issues.